Quick Links
Security researchers are investigating a large-scale phishing attack that targeted over 130 companies, including financial institutions, messaging services, and telecom operators. The extent of this hacking campaign, dubbed "0ktapus," may take several years to fully unravel.
For clarity, this phishing campaign has nothing to do with LastPass's recent data breach. But it is related to the Twilio and DoorDash attacks that were reported on August 8th and August 25th.
0ktapus Stole Nearly 10,000 Login Credentials
The 0ktapus phishing campaign focuses on major U.S. corporations, minus a few outliers based in other countries across the globe. And surprisingly, the list of 0ktapus targets includes Microsoft, AT&T, Verizon, Coinbase, and Twitter---again, these companies are targets, and we don't know if they were successfully hacked.
As of August 26th, Twilio and DoorDash are the only major companies that have announced an 0ktapus data breach. Both companies say that user data was accessed by hackers, though Twilio says that login credentials are safe. DoorDash warns that a small group of customers had their login and payment info stolen.
A Cloudflare report explains how the 0ktapus scheme operates. Basically, a ton of employees at targeted companies (including former employees) are sent "automated" text messages warning that their login information has expired. A link embedded in the text messages leads to a fake version of their employer's website, prompting the user to update their password.
Every company targeted in this campaign uses Okta Identity and Access Management services. And they all protect employee accounts using two-factor authentication (2FA). If an unknown device tries to log in to an employee's account, the employee receives a verification code on their phone.
So, 0ktapus' webpages imitate the Okta identification system. As an employee types their username and password into an 0ktapus webpage, it's automatically forwarded to a secret Telegram channel. Hackers take this information and try to log into an employee's account, triggering a 2FA verification process. The victim is asked to share a 2FA verification code from their phone, granting hackers access to a corporation's backend.
We Don't Know the Reason Behind These Attacks
This phishing campaign has a relatively clear narrative. Group-IB reports that 0ktapus initially targeted telecom companies, which may have provided the phone numbers for subsequent 2FA phishing attempts.
The majority of these phishing attempts were aimed at corporate employees. In theory, the group behind 0ktapus could have stolen anything from corporations, though current reports suggest that the group was after customer data. This information could be used in future attacks against businesses or individuals, but unfortunately, we aren't sure what the 0ktapus group obtained.
And this is where things get kind of frustrating; the 0ktapus campaign was a bit haphazard. Researchers at Group-IB call it "amateur," noting that the 0ktapus group failed to properly configure its phishing kit.
As we mentioned earlier, 0ktapus tricked people into sharing 2FA verification codes (and login data) with hackers. But these verification codes expire after just a few minutes, so hackers can't break into an account if they aren't quick enough. And evidently, the 0ktapus group sat in front of their computers all day to manually type in 2FA codes, rather than using a bot to automatically enter information and hijack accounts.
Additionally, victims of this phishing scheme were forced (by the phishing domains) to download an authentic version of AnyDesk. You know, a remote desktop software for PC. This software is completely useless when targeting people via text message.
We're frustrated that companies fell for an "amateur" phishing scheme. Especially one with such a clear paper trail.
Security Researchers May Have Identified a Hacker
Researchers at Group-IB have discovered 169 unique domains associated with 0ktapus. The majority of these domains are thinly veiled copies of corporate websites and use URLs like
http://att-mfa.com/
. (Don't visit this URL, but please observe that it uses HTTP instead of HTTPS---an obvious sign of phishing.)
Group-IB didn't need to go on a goose chase to find these domains. The group behind 0ktapus reused the same unique fonts, image files, and scripts on its phony websites. Once you discover a single 0ktapus domain, finding the rest is a piece of cake.
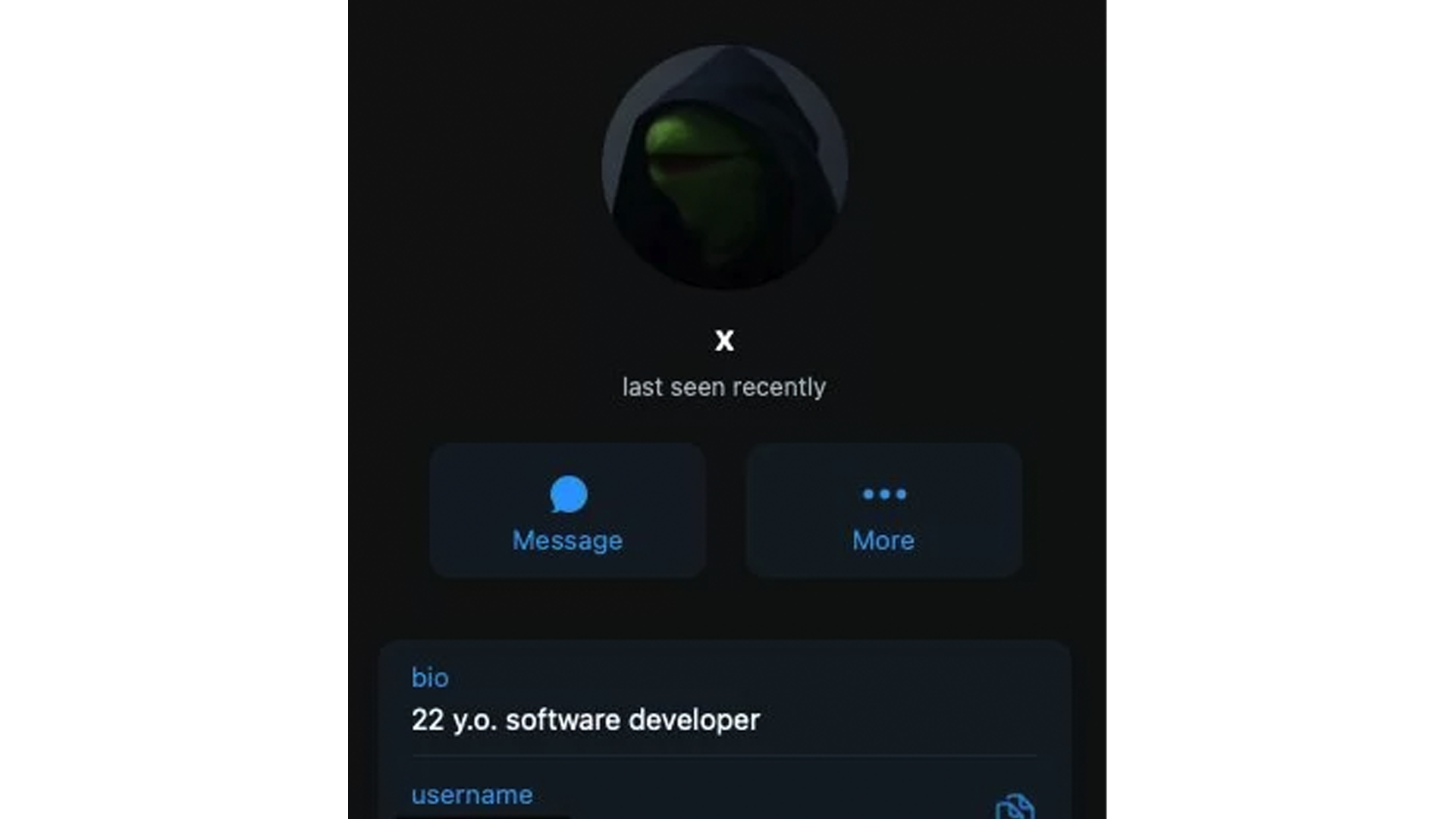
More importantly, Group-IB analyzed the 0ktapus phishing kit to find its associated Telegram channel. And one user in this channel, a 22-year-old programmer nicknamed "Subject X," was tracked and identified. Comments that "Subject X" left in other Telegram groups revealed their Twitter account and alleged location.
Despite the relative success of 0ktapus, it's clearly an amateur operation. That's great news for the authorities, but it's also a sign of that corporations aren't taking security seriously.
What Should You Do?
We still don't know enough about the 0ktapus campaign. Presumably, several companies need to come forward and announce that they were hacked. Given the breadth of this phishing scheme, it could take years for all of the details to come to light.
That said, we can only give you the usual advice:
- Inspect any URL that's sent via email or text message.
- Don't interact with websites that use HTTP instead of HTTPS.
- If someone sends you a work-related URL or request, verify that it's authentic with your employer.
- Enable two-factor authentication when possible.
- Use a password manager to generate unique login credentials for every website.
- If your job involves sensitive data, ask your company's security team about FIDO2 solutions, such as YubiKey.
- Add a fraud alert to your credit report to reduce the financial impact of identity theft.
These steps will significantly improve your security. They will also ensure that, in the event of a data breach, you can quickly respond and (hopefully) protect yourself.
Again, this is a developing story. We will update this article as we learn new information about the 0ktapus campaign. For up-to-date tech news, join our free newsletter.